Table of Contents
ToggleEver found yourself typing into a company system, thinking to yourself, ‘Why did I type my password in so many times?’ but then wondering how it came to be that this trust was created? Thus, the article about how does Kerberos authentication works will be useful in explaining the logic, flow, and anonymity of Kerberos in a pragmatic and career-related manner.
Besides, you will know how authentication tickets substitute passwords, why they fail, and why organizations use this protocol to have secure access. Consequently, you will have a clear picture of enterprise authentication, not the superficial definitions.
Understand the future of intelligent systems with what is agentic AI.
Understanding the purpose of Kerberos in modern networks
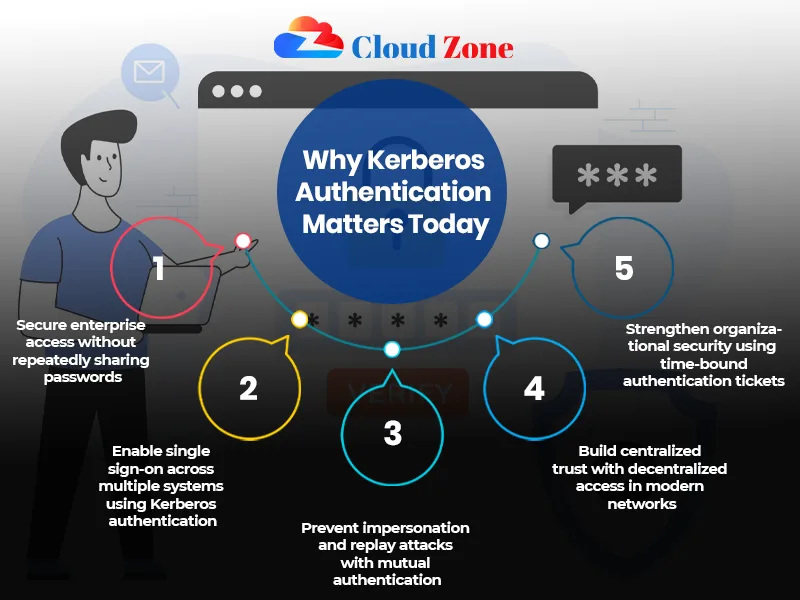
Kerberos was developed with the intention of addressing a trust issue in distributed systems. Thus, it does not transfer passwords through the network, but it uses cryptographic tickets that are issued by a trusted authority. In addition, when professionals present a question of what is Kerberos authentication, they usually fail to understand its fundamental value, which is centralized trust and decentralized access. Therefore, the systems identify users one time, and then safely reuse the trust. In such a way, Kerberos minimizes attack surfaces and enhances user experience in large environments.
Moreover, Kerberos also allows users and services to authenticate each other, thus eliminating the attacks of impersonation. Moreover, it provides scalability, which enables thousands of clients and services to be used safely in the same network. Lastly, understanding what is kerberos authentication in this centralized trust and decentralized access is useful in ensuring that IT professionals develop more resilient and secure enterprise environments.
Gain insights into data monitoring with our guide on telemetry.
Core components that make Kerberos work
- First, the Authentication Server authenticates the user identity.
- More than that, the Ticket Granting Server is issuing the service-related tickets. Moreover, clients and services are based on a common Key Distribution Center.
- Such as, to give an example, this architecture provides the answer to the question of what Kerberos authentication really is in enterprise security.
- Consequently, all access requests have a managed and an audit trail.
Find out the top roles that pay well with our guide on the highest paying jobs in India.
Build kerberos authentication expertise with hands-on labs and cases
The step-by-step authentication flow explained
The Kerberos process has a specific sequence. Thus, the client will initially authenticate without revealing its password. Besides, the system sends out a Ticket Granting Ticket after validation. This leads to the user reusing such a ticket and accessing several services safely. This flow therefore shows how does Kerberos authentication works in real operating situations as opposed to theory.
This process also takes care of the procedure where credentials are never sent throughout the network several times, minimizing the chances of getting intercepted. Also, the lifetime of all service tickets is limited, which introduces an additional level of protection. Lastly, the knowledge of this chain will enable IT specialists to better troubleshoot authentication problems and streamline access controls.
Discover flexible infrastructure options with hybrid cloud.
Why pre-authentication exists and why it matters
- First, the pre-authentication prevents offline password attacks.
- Furthermore, customers should demonstrate awareness of a secret to obtain a ticket.
- Moreover, the failures could be presented as a form of Kerberos pre-authentication failed in logs.
- As an example, such failures can be caused by incorrect time synchronization.
- Consequently, administrators obtain early warnings of security or configuration challenges.
Discover opportunities and growth with women in cloud Azure training opportunities.
Common causes behind Kerberos authentication failures
The failures have seldom just happened. Thus, improperly configured time clocks, ineffective encryption preferences, or expired tokens tend to create havoc. Additionally, administrators often experience Kerberos pre authentication failed messages when doing migrations. In turn, such mistakes are an indication of broken trust, but not an instance of accidental logins. Failure patterns are therefore known to enhance security response and reliability in a system.
Strengthen your cloud skills with AWS Skill Builder.
Also, tracking of such failures aids in preemptively detecting possible security threats. Moreover, recording the recurring cases simplifies troubleshooting of subsequent cases. Lastly, eliminating the cause of the errors of Kerberos pre authentication failed helps in improving the stability of the network and the confidence of the user.
Monitor and optimize your apps using Amazon CloudWatch.
Practice kerberos authentication through real cybersecurity project implementations
Security advantages beyond single sign-on
- What Kerberos authentication does is that it reduces the network exposure of passwords.
- Also, mutual authentication secures services and users.
- Moreover, the replay attacks can be much more difficult.
- For instance, a professional with knowledge of what is Kerberos authentication will be aware of its use in zero-trust measures.
- As a result, this makes organizations use Kerberos as a platform of layered security.
- Therefore, there will be no Kerberos pre authentication failed messages while applying.
Explore intelligent solutions with Azure AI and machine learning services.
Kerberos in cloud and hybrid environments
Kerberos is not a stagnant product. Thus, the contemporary implementations are combined with the providers of cloud identities and hybrid systems. Furthermore, this development justifies how does Kerberos authentication works with services that are taken out of the premises. Therefore, trust is still enforced by tickets, whereas identity systems grow. Therefore, Kerberos can still be used even with changes in architecture.
Additionally, Kerberos is also multi-factor-authenticated and compatible with the current encryption standards, and can be improved in terms of security. In addition, it facilitates seamless single sign-on between various applications that lessen the end user burden. Lastly, by knowing such updates, IT professionals will be in a position to deploy Kerberos successfully in both traditional and modern environments.
Kickstart your cloud career with AWS certification training (Amazon Web Services).
Diagnosing and resolving authentication issues
- First, logs of Kerberos pre-authentication failed are reviewed by administrators.
- Also, they check time synchronization and compatibility of encryption.
- Also, correct service principal setup eliminates the occurrence of repeat failures.
- The example is that the error of Kerberos pre authentication failure can be resolved and access is usually restored automatically.
- Consequently, any systematic troubleshooting minimizes downtime and risk.
Advance your container expertise by mastering Azure Kubernetes Service.
Why Kerberos knowledge matters for IT professionals
Kerberos is not a protocol; it is a skill that you can become proficient in in your career. Consequently, practitioners with knowledge of what Kerberos authentication can communicate better with security departments. In addition, the knowledge enhances the decision on incident response and system design. Therefore, companies appreciate engineers who have a deep understanding of authentication flows. Therefore, the technical credibility over an extended period is boosted by knowledge of Kerberos.
The Kerberos knowledge can also assist professionals to predict and avert security intrusions before it affects the operations. Moreover, it allows a smooth transition to such developing technologies as cloud-based services and hybrid identity. Lastly, the knowledge of Kerberos provides a bridge to learn other advanced authentication schemes and thus, IT specialists become multidimensional and more sought after.
Upskill confidently with AWS training for non-tech professionals.

Conclusion: Kerberos as a foundation of enterprise trust
To sum up, controlled trust is the basis of secure authentication, and not repeated passwords. Additionally, knowledge of failure, such as Kerberos pre-authentication failed converts the errors into information. Therefore, understanding the functionality of this authentication will enable professionals to build, protect, and troubleshoot multifaceted systems with confidence. Therefore, Kerberos is one of the most important blocks of the contemporary enterprise security, and how does Kerberos authentication works is something every serious IT professional must grasp well.
Compare top cloud platforms with our Azure vs AWS vs Google Cloud guide.
Gain network security control today. Furthermore, by practicing Kerberos, you would avoid authentication failures, protect sensitive data, and debug problems effectively. That is why, begin studying how does Kerberos authentication works and convert this necessary protocol knowledge into a great career skill.
Protect your infrastructure by learning the importance of AWS security training.

Sukhamrit Kaur
Sukhamrit Kaur is an SEO writer who loves simplifying complex topics. She has helped companies like Data World, DataCamp, and Rask AI create engaging and informative content for their audiences. You can connect with her on LinkedIn.



